Information Security, Cybersecurity and System Availability
Challenges and Commitments
In an era where information technology is advancing rapidly and becoming integral to global business operations, cybersecurity threats have emerged as a critical concern for all organizations.
GGC recognizes the importance of safeguarding data and technology systems from both external threats and internal data leakage, which may affect operational continuity and the security of information related to Employees, Customers, and Suppliers and Business Partners. To address these risks, GGC strengthens its information technology governance structure, strictly complies with personal data protection laws, and provides continuous training to Employees to enhance knowledge, understanding, and awareness regarding cyber security.
Key Stakeholders
Employee
Customer
Government
Supplier and Business Partner
For additional information on stakeholder engagement: Stakeholder Engagement
Goals
Key Performance in 2025
Management Approach
GGC has established an Information Technology Security Policy as a framework for developing a systematic information security management system, aligned with international standards such as ISO/IEC 27001 for Information Security Management and the Control Objectives for Information and Related Technologies (COBIT). The policy also incorporates clear operational procedures to enhance cybersecurity management, prevent undesirable incidents, and reduce risks and potential impacts on the organization effectively.
The Structure of Overseeing Information and Cyber Security
GGC has established a governance structure for information and cyber security comprising three main levels: Board Level, Management Level, and Operational Level. Each level holds specific roles and responsibilities to oversee, audit, and manage information security risks effectively and systematically.
| Governance Level | Roles and Responsibilities |
|---|---|
| Board Level Audit Committee |
|
| GC Group’ s Digital & IT Steering Committee (DISC) |
|
| ISMS Committee |
|
| Enterprise Architecture (EA Committee) |
|
| Chief Information Security Officer: CISO |
|
| Management Level |
|
| Operation Level |
|
Mitigation Actions for Cyber Threats and Information Leaks
Independent External Audit of the IT Infrastructure and/or information security management system inspections
GGC, in collaboration with PTTGC, conducted an assessment in accordance with ISO/IEC 27001:2013 to ensure that GGC’s Information Security Management System (ISMS) operates effectively and aligns with international standards. The external audit scope covers Infrastructure as a Service, Infrastructure as a Service on Cloud, Internet Gateway Zone Management, and Application Management, which also plays a key role in supporting the external recruitment process.
Information and Cyber Security Management Program
GGC continuously enhances Information Security and Cyber Security through the development of security audit plans and the adoption of advanced information security technologies to address rapidly evolving cyber threats. GGC has developed a five-year IT Action Plan (2023–2027), identifying Cyber Security as a key priority, supported by clear and comprehensive operational guidelines.
The primary objective of this plan is to ensure that the Cyber Security program is regularly updated and maintained in alignment with international standards and best practices, thereby enabling secure and efficient business operations. Key activities under this plan include:
- Process and infrastructure assessment
- System enhancements to address vulnerabilities, including risk assessment scanning
- Phishing tests and tailor-made programs for specific functions
- Data Governance for GGC (Data Protection and Data Classification)
Process and Infrastructure
GGC has established an Information Security Management System (ISMS) in alignment with international standards and adopted asset security practices consistent with Cyber Security requirements. External agencies conduct annual inspections and reviews of GGC’s information and cyber infrastructure. The most recent inspection confirmed that all processes and infrastructures fully comply with international standards, with no issues or defects identified.
As a subsidiary of PTTGC, GGC has adopted the Cyber Drill Procedure as a standard operational guideline for all IT personnel. This ensures effective and secure incident response to IT or Cyber Security-related events while minimizing potential damage. Cyber drills are conducted at least twice a year, once during January–June and once during July–December.
GGC has also established an IT Security and Cyber Security Disaster Recovery Plan outlining procedures for responding to disasters affecting the primary data center. The plan specifies recovery timelines for various information types and detailed steps for resuming normal business operations. Disaster recovery testing is conducted at least twice a year during the same periods as the Cyber Drill to strengthen preparedness and response efficiency.
Vulnerability Assessment
GGC conducts external vulnerability assessments at least twice a year to evaluate risks and identify system improvement opportunities. The Business Continuity Plan is implemented to support operations during emergencies. In 2025, GGC conducted its annual Cyber Incident Response Tabletop Exercise to assess the stability and effectiveness of information and Cyber Security systems. The exercise simulated a cyber-attack by external intruders attempting to penetrate GGC’s IT security and gain access to sensitive information, posing a risk of data leakage. Each Vulnerability Assessment (VA) covers critical areas, including:
- Clickjacking
- Cookies not marked as HTTP Only
- Cookies with missing, inconsistent, or conflicting properties
- Programming error messages
- Version disclosure
- Content Security Policy misconfiguration
- Permissions-Policy header not implemented
- Clickjacking
GGC also performs internal and external vulnerability scans every six months to support protection and remediation planning. Vulnerability Severity Levels are categorized into three levels: High, Medium, and Low.
Information Security and Cybersecurity Awareness
GGC has strengthened awareness and readiness on Cyber Security for Employees at all levels by providing online learning (E-Learning) on the topic “Cyber Security Online”, accompanied by post-learning assessments to evaluate understanding. This enables Employees to effectively apply the acquired knowledge in their daily work.
Training & Boost-Up Program
The Training & Boost-Up Program is an online training initiative designed to align with the roles and responsibilities of each Employee and extended to Suppliers and Business Partners. The program incorporates performance indicators to assess learning outcomes. Where assessment results fall below the defined threshold, additional training is arranged to reinforce understanding and readiness in Cyber Security.
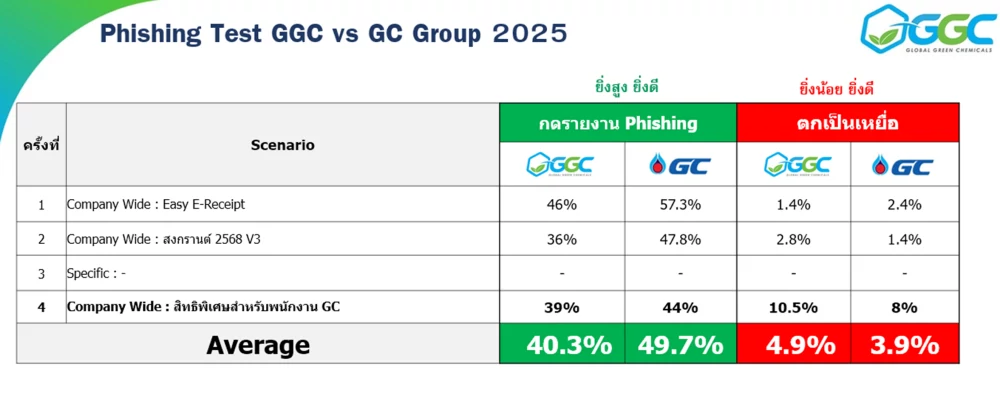
In 2025, GGC conducted a Phishing Test to assess Employee awareness and response to email-based threats. Employees who were unable to correctly identify and report Phishing emails were required to attend additional training to enhance their capability in managing Information Security risks
Outcomes and Benefits
- Employees are better prepared and more vigilant toward Cyber Security threats.
- The organization’s security systems have greater resilience and responsiveness to emerging risks.
- Potential long-term damage from Cyber Attacks is reduced.
Power BI Workshops

In 2025, GGC organized more than two Power BI training sessions for Employees in the GC Group during August and September. The workshops focused on helping participants understand data connectivity, the creation of interactive dashboards, and the design of visualizations that effectively communicate business insights through full-day, hands-on learning.
Subsequently, GGC continued training under the “Next-Level Insights with Power BI” program to elevate Employees’ Power BI capabilities to an intermediate level, with emphasis on advanced Power Query, advanced DAX, interactive report design techniques, and guidelines for publishing reports via Power BI Service.
Outcomes and Benefits
- Participants are able to independently design and develop Power BI dashboards.
- Participants understand key DAX and Data Modelling principles for in-depth data analysis.
- A learning network and community of practice in Data Analytics has been strengthened.
GGC AI Jump Start
The GGC AI Jump Start program was held on 13 June 2025 via Microsoft Teams with the objective of promoting and accelerating the practical adoption of Artificial Intelligence (AI) within the organization under the AI Adoption Framework, which covers three dimensions: People, Process, and Technology.
The program featured in-depth presentations and live demonstrations of Generative AI and Microsoft Copilot, along with guidance on License Management and real-life case studies showcasing AI applications in end-to-end work processes.
Outcomes and Benefits
- More than 80 Employees and related functions participated.
- Participants gained structured and secure understanding of AI adoption within the organization.
- Participants identified practical opportunities to apply Generative AI and Copilot to improve work efficiency.
Data Storytelling Workshop

The Data Storytelling Workshop was organized to enhance and develop skills in presenting business data in the form of “Data Storytelling” for Employees within the GC Group, thereby increasing their capability in effective data-driven communication. Participants received knowledge on data analysis and interpretation using the Problem–Reason–Action Framework, dashboard design that clearly conveys key insights, and tailoring presentations to different Stakeholder groups. This contributes to business value creation and strategic impact for the organization.
Outcomes and Benefits
- Participants can transform technical data into simple, compelling narratives that support business decision-making.
- Participants strengthened skills in Visual Communication and Dashboard Design for effective data presentation.
- The workshop supports the development of strategic thinking and innovation through the use of data.
IT/OT Convergent
The IT/OT Convergent project aims to integrate Information Technology (IT) and Operational Technology (OT) systems to operate seamlessly and efficiently. The initiative enhances operational agility, improves real-time, data-driven decision-making, reduces costs by improving efficiency and minimizing system downtime, strengthens security through centralized management, and enables the organization to adopt new innovations and technologies effectively.
The implementation roadmap is divided into several phases: planning and system assessment during Months 1–2 (including Cisco Security and Palo Alto Network assessments); system architecture design and security control planning during Months 3–4 (based on guidance from Gartner and the Purdue Model); followed by pilot deployment, broader implementation, Employee training, continuous monitoring, feedback collection, and iterative improvements for long-term scaling.The project also defined four Quick Win OT Security controls:
- Building a Cyber Security culture through the establishment of an OT Security Policy.
- Conducting OT Cyber Assessment to evaluate OT system Cyber Security.
- Piloting Smart Vibration Proof of Concept (PoC) to detect equipment anomalies as a preventive measure.
- Considering the SAM GUARD PoC to monitor and detect anomalies in ICS/SCADA systems, thereby enhancing the ability to prevent and respond to Cyber Security threats comprehensively.

Outcomes and Benefits
- Improved operational efficiency and reduced unplanned downtime.
- Strengthened OT security in line with international standards.
- Enhanced readiness for innovation and the digital transformation journey.
Supplier risk explorer
Supplier Risk Explorer is a strategic risk management tool used within the GC/GGC Group to systematically monitor, prevent, and mitigate risks arising from Suppliers and Business Partners. It includes ongoing tracking of risk indicators and compliance, as well as blocking high-risk emails and domains to enhance communication security. The tool also compares risk profiles with the PTT/GC Group to align with best practices.
Regarding the 2025 Cyber Security Resilience Survey, the Stock Exchange of Thailand (SET) officially postponed the survey to allow listed companies additional time to implement recommendations from the 2024 assessment. Should the survey be conducted again in 2026, advance notice will be provided. The survey forms part of a broader Cyber Security strengthening initiative, which includes adoption of the NIST framework, participation in PTT Group programs, and internal campaigns to raise awareness on phishing.
Outcomes and Benefits
- Reduced risks from Suppliers and Business Partners through proactive monitoring and analysis.
- Enhanced Cyber Security and communication security within the organization.
- Alignment with PTT/GC Group practices, reinforcing system resilience and stability.
Reporting Process for Cyber Attack Indicators and Data Leakage Incidents
GGC has established procedures for reporting incidents, vulnerabilities, or suspicious activities, including Phishing Email alerts. The reporting process is initiated immediately when users or Employees detect such incidents, and the response follows the defined steps below.
Employee Report on Cyber Attack
- A user detects a Phishing Email and reports it to the Service Desk.
SOC Team Investigates the Incident
- The Service Desk escalates the report to the SOC Team.
- The SOC Team determines the severity level: Low Severity or High Severity (in the latter case, the incident is escalated to the SOC Manager and TF-IT Security Team).
SOC Team Coordinates Mitigation
- The SOC Team develops a mitigation plan.
- The SOC Manager informs the Communication Team that Phishing activity has occurred.
TF-IT Security Evaluates Outcomes
- After mitigation is complete, TF-IT evaluates the results and confirms system stability.
SOC + TF-IT Prepare Final Report
- Once the situation returns to normal, the SOC and TF-IT Security Teams prepare a final incident report.
- The Communication Team informs the organization that the issue has been fully resolved.
In 2025, a total of 277 Employees participated in the Phishing Test. Of these, 107 Employees correctly reported Phishing emails, accounting for 40.3% of all participants, while 4.9% of Employees fell victim to Phishing emails